What Changed and Why It Matters
A new toolchain for autonomous AI agents is taking shape. It spans build, test, deploy, observe, and secure—inside the systems companies already use.
The signal: major platforms are shipping lifecycle tools, developer workflows are becoming agent-first, and security vendors are warning about new attack surfaces. Research is also improving agent planning and tool use.
Here’s the part most people miss. The moat won’t be a bigger model. It will be distribution into existing toolchains, reliable execution, and trust.
Agents don’t just need IQ. They need interfaces, permissions, memory, and tests.
The Actual Move
Several concrete moves point to an emerging stack:
- Google introduced ADK aimed at running agents inside DevOps toolchains. It provides direct paths to operate tools like GitHub, Jira, and MongoDB. Where that path is missing, MCP-based integrations fill gaps. The emphasis is clear: plug agents into the tools developers already trust.
- Salesforce launched Agentforce Workbench, a lifecycle management toolchain for building, testing, and deploying autonomous agents at enterprise scale. It targets governance, evaluation, and safe rollout—enterprise must-haves.
- Amplify Partners outlined the “agent-first developer toolchain,” arguing the SDLC will re-center on agents. Expect new abstractions, observability, evaluation harnesses, testability, and infra purpose-built for AI-first development.
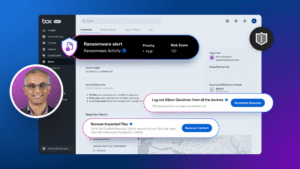
- Security research from CrowdStrike highlights “agentic tool chain attacks.” Threats include compromised tools, over-permissive actions, data exfiltration, and prompt-layer exploits. The message: apply least privilege, isolation, and rigorous validation.
- Tooling momentum continues. Feature-automation agents integrate with Azure DevOps and existing Microsoft stacks; swarms like Beam AI coordinate multiple agents for complex tasks; open-source frameworks help teams assemble agent workflows and tool adapters faster.
- On the research front, ToolChain* proposes a tree-search planning method that helps agents navigate large tool action spaces more efficiently. Better planning yields fewer blind actions and higher reliability.
The stack is converging: protocol, runtime, tool adapters, evaluation, and guardrails.
The Why Behind the Move
This shift is about operationalizing agents, not just prototyping them. Here’s the builder view.
• Model
Foundation models are strong enough. The bottleneck is orchestration: tools, context, memory, plans, and review loops. Planning algorithms and MCP-style interfaces reduce friction.
• Traction
Agents that live where work happens—GitHub, Jira, MongoDB, Azure DevOps, Salesforce—get immediate usage. Embedding into the daily workflow beats standalone pilots.
• Valuation / Funding
Capital follows operational leverage. Platforms that convert agent demos into measurable productivity and safer change management will attract enterprise budgets.
• Distribution
The winning route is distribution into existing toolchains and ecosystems. Native integrations minimize switching costs and accelerate trust.
• Partnerships & Ecosystem Fit
MCP and direct adapters expand tool coverage fast. Cloud platforms and enterprise apps become natural hubs for agent governance, identity, and data access.
• Timing
We’re entering the “make it work reliably” phase. Lifecycle management, evaluation, and policy are the keys to scaling beyond pilots.
• Competitive Dynamics
- Clouds and enterprise platforms offer lifecycle, security, and data gravity.
- Open-source frameworks innovate execution, swarms, and planning speed.
- Security vendors harden the toolchain and reduce blast radius.
Expect co-opetition: open frameworks drive innovation; platforms drive standardization and adoption.
• Strategic Risks
- Toolchain attacks and over-permissioned agents
- Silent failures without evaluation and observability
- Vendor lock-in vs. interoperability
- Compliance, auditability, and data governance gaps
Reliability—backed by tests, policies, and telemetry—will separate pilots from production.
What Builders Should Notice
- Put agents where the work lives. Integrate with GitHub, Jira, CRM, and CI/CD.
- Treat agents like software systems. Add tests, evals, logging, and rollback.
- Permissions are product. Default to least privilege and human-in-the-loop for risk moves.
- Interop compounds. Support MCP and common tool adapters to widen coverage fast.
- Planning matters. Tree-search, review loops, and retries increase success per action.
Buildloop reflection
The future of agents isn’t smarter prompts. It’s safer, observable execution.
Sources
- DevOps.com — Google ADK Opens the Door to AI Agents That Work Inside Your DevOps Toolchain
- Amplify Partners — The agent-first developer toolchain: how AI will radically transform the SDLC
- Salesforce Newsroom — Salesforce introduces Agentforce Workbench_ First-of its-kind AI agent lifecycle management toolchain for building, testing, and deploying autonomous AI agents at scale
- Rising Tide Partners — Shipping with AI – by Neal Bloom
- CrowdStrike — How Agentic Tool Chain Attacks Threaten AI Agent Security
- AugmentCode — 5 Autonomous Agents for End-to-End Feature Automation
- Medium — AI Agent Automation Tools: Trends and Beginner Recommendations
- arXiv — ToolChain*: Efficient Action Space Navigation in Large Tool Spaces