What Changed and Why It Matters
AI incidents are rising faster than organizations can respond. The gap isn’t just technical. It’s operational.
“Incident response doesn’t fail because of the attack. It fails because the organization cannot operate at the speed the attack demands.” — BreachRx
Several signals now point to the same conclusion: AI needs its own CERTs—Computer Emergency Response Teams—but purpose-built for model failures. Reported AI harms climbed sharply, with one industry source citing a 56.4% year-over-year increase. Policy groups are calling for national AI incident response capacity. Enterprise vendors are reframing IR around data governance and architecture. And independent teams are publishing playbooks for AI-specific failure modes.
Here’s the part most people miss: the majority of AI failures won’t look like cyber intrusions. They’ll look like silent regressions, misaligned agents, poisoned data, and degraded pipelines. Traditional SOC workflows don’t catch these fast enough.
The Actual Move
The market is converging on an AI CERT pattern—specialized teams, tooling, and runbooks to detect, triage, contain, and recover from model failures.
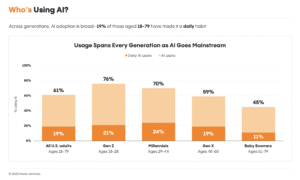
- Market data and urgency: Industry reporting flags a 56.4% YoY rise in AI harms, while a separate security update claims a 45% surge in AI-driven incidents over 18 months. Both underscore accelerating volume and complexity.
- Policy momentum: Think tanks urge U.S. preparedness for AI system failures and stronger federal action on AI incident response. This mirrors broader moves toward formal reporting and coordinated response.
- Enterprise architecture focus: Security leaders emphasize that AI IR success hinges on upstream investments—training data governance, robust security architecture, and readiness-by-design.
- Playbooks and automation: New guidance contrasts physical fail-safes (sprinklers, generators) with the near-total absence of automatic responses for AI failures. Emerging tools pitch “smarter response, less downtime” by automating detection, rollback, and guardrail enforcement.
- Risk framing: Research groups warn that future loss-of-control incidents could disrupt essential services and infrastructure, expanding incident response from IT risk to societal resilience.
- Production reality checks: Practitioners highlight how “95% accurate” models can still fail in production due to drift, stale features, and infrastructure blind spots—problems classic monitoring misses.
“Physical failures trigger automatic responses. Sprinklers activate. Emergency lighting engages. Backup generators start. AI incidents trigger …” — Cognitive Corp
“Future critical failures from advanced AI models could trigger widespread disruptions across essential services and infrastructure networks.” — RAND Europe
The Why Behind the Move
AI CERTs are not a branding exercise. They’re an operating model for model risk.
• Model
AI systems fail differently: drift, data poisoning, jailbreaks, hallucinations, bad tool use, and brittle pipelines. That demands IR built around model lineage, feature health, eval harnesses, guardrails, and kill switches.
• Traction
Incident volume and severity are climbing. Claims of 56.4% YoY harm growth and a 45% incident surge align with what teams see in production: more autonomy, wider blast radius.
• Valuation / Funding
Budget will shift from generic MLOps to AI risk and reliability. Expect new spend on detection, containment, rollback, post-incident audit, and compliance reporting. The winners will tie reliability to direct cost savings and regulatory readiness.
• Distribution
Go-to-market runs through CISOs, CTOs, and Heads of Risk. Land in existing security and observability stacks (SIEM, SOAR, APM) while plugging the model-awareness gap: data lineage, feature drift, eval results, and agent behaviors.
• Partnerships & Ecosystem Fit
Tight integrations with cloud AI services, vector DBs, model registries, feature stores, prompt/guardrail layers, and ticketing systems. Alliances with cyber IR firms, red teams, and audit providers will accelerate adoption.
• Timing
Regulators are moving toward incident reporting and safety cases. Enterprises are scaling copilots and agents across workflows. The attack surface is growing right as oversight expectations harden.
• Competitive Dynamics
- Cyber IR incumbents: great at intrusion and malware, thin on model context.
- MLOps vendors: strong on pipelines, weak on incident-grade triage/containment.
- New entrants: credibility hinges on measurable MTTA/MTTR improvements for AI-specific failures.
• Strategic Risks
- Over-automation: “self-healing” that hides root causes or amplifies harm.
- High false positives: alert fatigue will kill org trust.
- Data exposure: incident logs and prompts may leak sensitive content if mishandled.
- Vendor lock-in: proprietary evaluators without exportable evidence impede audits.
“The organizations that respond effectively are the ones that invest beforehand – in training data governance that enables …” — Cisco
What Builders Should Notice
- Treat model failure as an ops problem. Stand up an AI CERT: IR lead, SecOps, MLOps, SRE, Legal, Risk, Comms.
- Instrument the right metrics: MTTA/MTTC/MTTR for AI, drift deltas, unacceptable output rate, guardrail hit rate.
- Build kill switches and blast radius controls: canary rollouts, shadow mode, circuit breakers for tools and agents.
- Make evidence portable: log prompts, context, model versions, features, eval results. You’ll need them for audits and RCA.
- Shift-left on governance: data provenance, red teaming, and pre-deploy evals reduce incident odds more than any after-the-fact patch.
Buildloop reflection
“Reliability is a product decision. Incident response is how you ship it every day.”
Sources
BreachRx — AI Will Break Incident Response. Mythos Just Proved It.
AICerts — AI harms see 56.4% YoY increase, raising urgent oversight
The Future Society — AI Incidents Are Rising. It’s Time for the United States to …
Cisco Blogs — Your AI incident response success relies on security architecture
Cognitive Corp — When Building AI Fails: The Incident Response Playbook Nobody Has
Riseup Labs — AI Automation for Incident Response
Medium — The Hidden AI Infrastructure Failure Problem: Why Your 95% Accurate Model Is Silently Breaking Production
RAND Europe — Examining risks and response for AI loss of control incidents
LinkedIn — AI-driven incidents surge 45% in 18 months, reshaping IR …